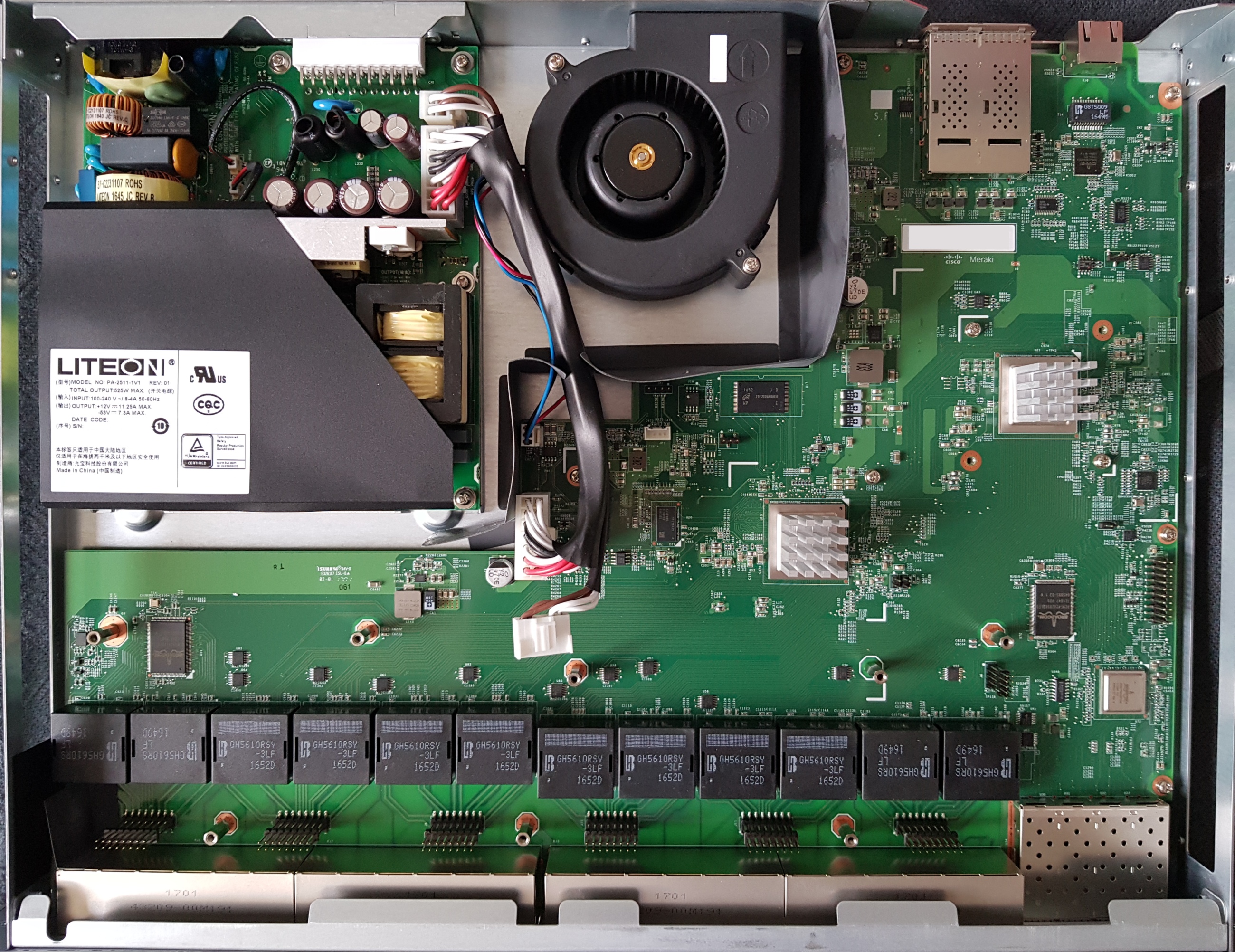
The Meraki MS210 and MS225 series switches offer 24 or 48 ports of Gigabit Ethernet, four SFP/SFP+ uplink ports, a dedicated remote management port, and stacking capabilities via QSFP.
Here is a quick summary of the MS210/MS225/MS250 specs:
- Broadcom Broadcom BCM56160 “Hurricane3” ASIC
- Broadcom BCM82756 10G PHY
- Broadcom BCM59121 PSE controller (PoE models only)
- 16MB of SPI flash (MX25L12805D)
- 1024MB DDR4 RAM (soldered)
- 256MB of NAND (MT29F2G08ABAEAWP)
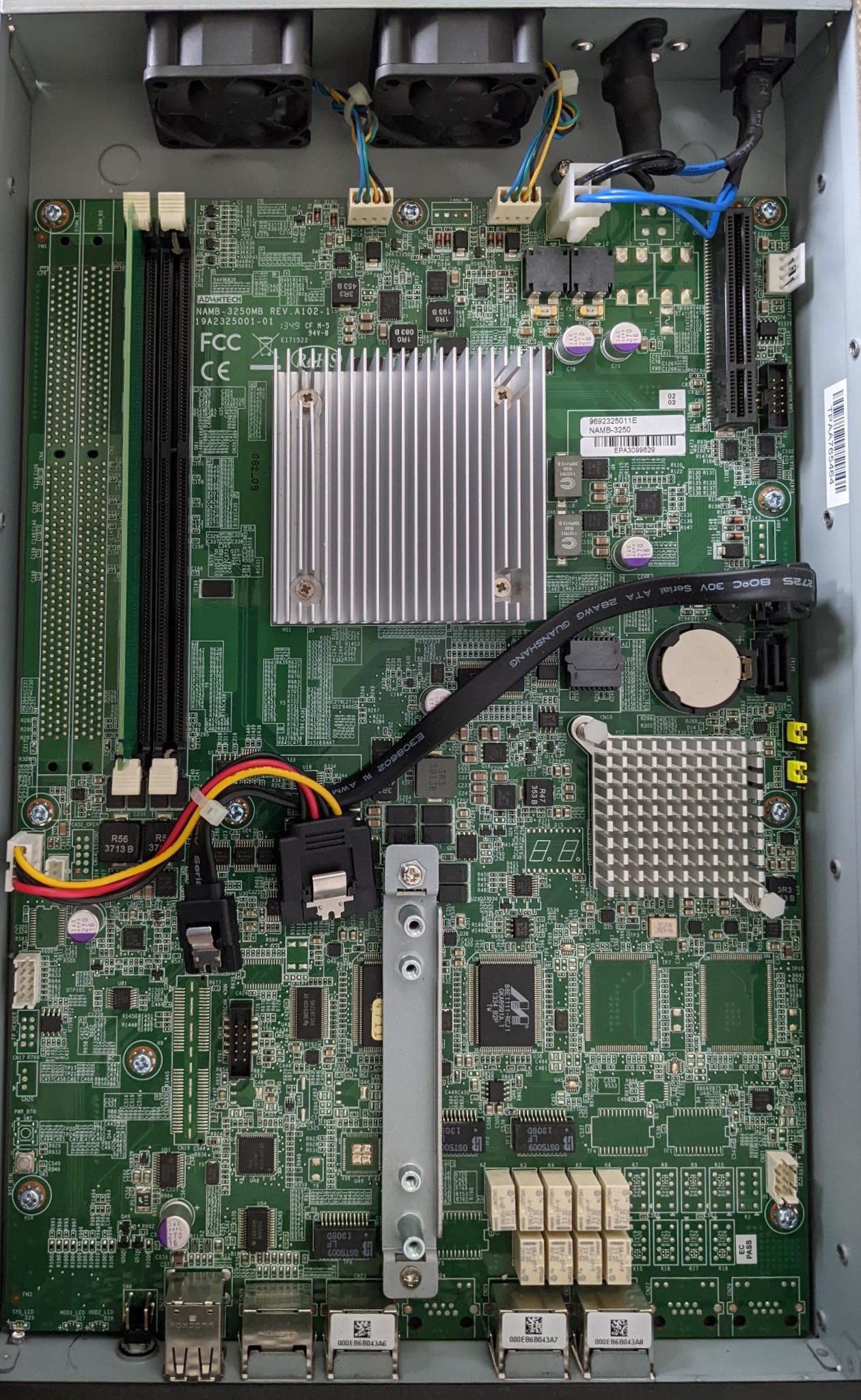
The Meraki codename for the MS210, MS225, and MS250 series is “brumby” and all brumby switches run the same firmware release (switch-arm). The MS250 is essentially the MS225 with hot-swap power supplies (similar to the MS220/MS320).
Keen readers may be wondering why the MS210 series has only SFP ports while the MS225 has SFP+ ports, given they are identical hardware and run the same switch-arm firmware. The answer is market segmentation; Meraki decided to artificially limit the speed of the MS210 SFP ports to 1G, even though the MS210 hardware is capable of 10G via SFP+. Early in the boot process switch_brain checks the switch model, and if it identifies as the MS210 series the SFP port speed is limited to 1000M.
The stock Meraki boot process uses u-boot on SPI to load a “bootkernel” (also from SPI), which then initializes NAND and using kexec boots the main firmware. The firmware layout follows the standard Meraki practice of having A/B firmware images: bootkernel1, bootkernel2, part.safe, part.old.
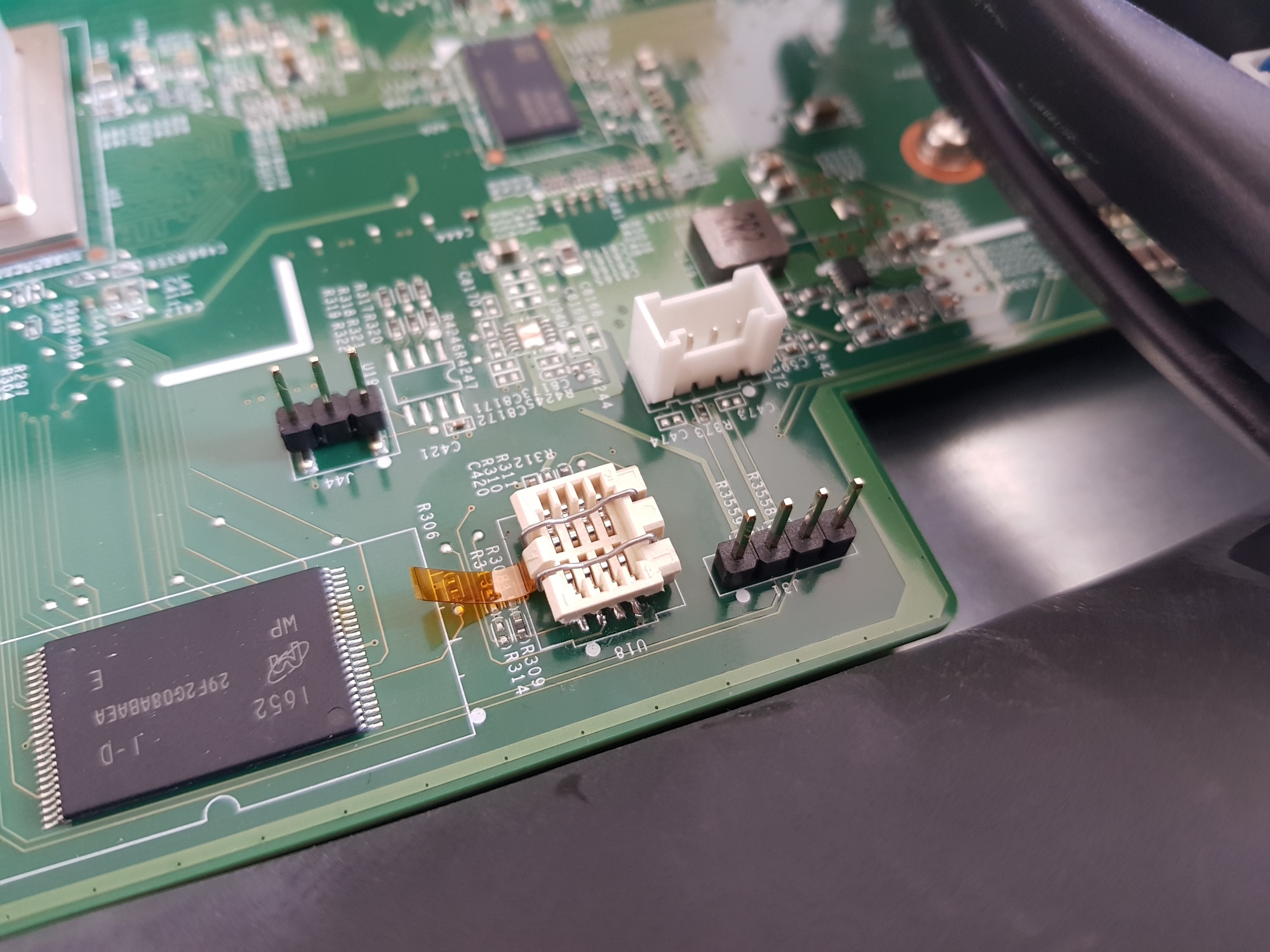
If you wish to flash your MS210/MS225, you will need to remove or socket the SOIC8 SPI flash (U18). This is because the ASIC is powered by the same +3.3V voltage rail as the SPI flash, and will attempt to boot when you attach your flashing device, which interferes with your ability to read/write the contents of flash. I prefer the Wieson G6179-10 SOIC8 socket (available from Adafruit). People outside the US will probably find it easier to desolder the flash and use a SOIC8 socket with prototype wires, as the G6179-10 is difficult to obtain for a reasonable price.
Unlike the MS120, the MS210/MS225 do not implement secure boot, so all that is needed to develop on the platform is to recompile and flash u-boot from the Meraki GPL release and then interrupt the boot process and provide your own firmware build (e.g. via TFTP).
The UART header is J31 on both the 24 and 48 port models and follows the standard Meraki UART pinout (1: VCC/3.3V, 2: Tx, 3: Rx, 4: GND) at 115200 baud.
The Broadcom SDK for the BCM56160 series implements the packet engine in userspace, using the linux_kernel_bde and linux_user_bde kernel modules to interface with the ASIC. In the Meraki firmware, the packet engine is a component of the userspace click daemon, which loads the bcm_click shared object during click router initialisation.
There are no public datasheets available for any of the Broadcom chips used in the MS210/225. While you can find information on OpenBCM, as far as I can tell the API provided by OpenBCM (via the kernel modules) which is used to implement the packet engine has no public documentation. If anyone has more information, please get in touch 😀
| Model | Meraki Board | Part number |
|---|---|---|
| MS210-24 (P) | BRUMBY_24 | 600-58015 (P: 600-58025) |
| MS210-48 (LP/FP) | BRUMBY_48 | 600-58035 (LP: 600-58045, FP: 600-58055) |
| MS225-24 (P) | BRUMBY_24 | 600-58010 (P: 600-58020) |
| MS225-48 (LP/FP) | BRUMBY_48 | 600-58030 (LP: 600-58040, FP: 600-58000) |
| MS250-24 (P) | BRUMBY_24 | 600-58050 (P: 600-58060) |
| MS250-48 (LP/FP) | BRUMBY_48 | 600-58070 (LP: 600-58080, FP: 600-58090) |